Furl is currently in closed beta. All organizations and users will be initially provisioned by the furl team. Reach out to support@furl.ai if you believe there is an issue with your account or organization setup.
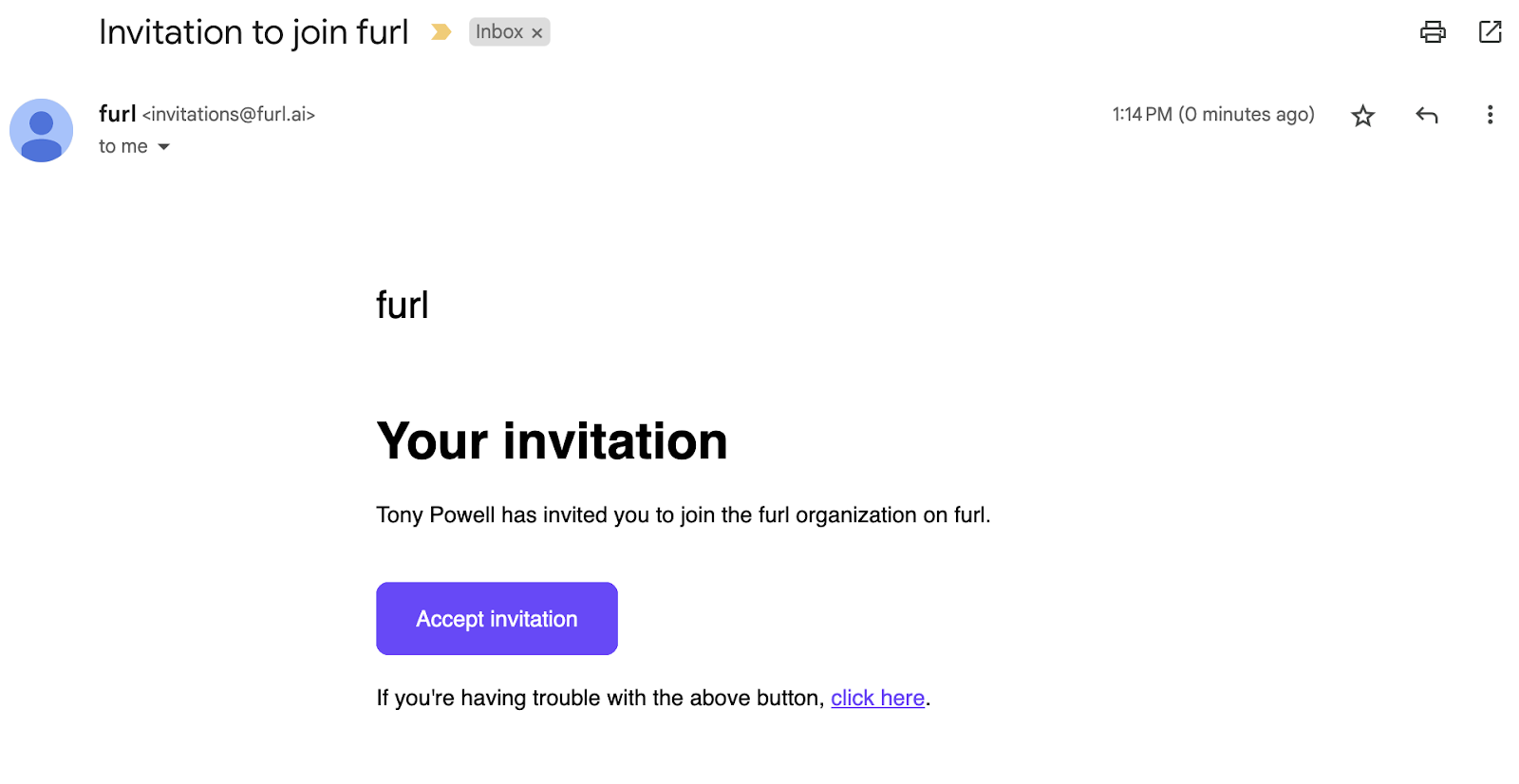
Once furl has provisioned your organization, users will receive an email invitation to join. Users can then authenticate using their Google account or with a one time password to registered email.
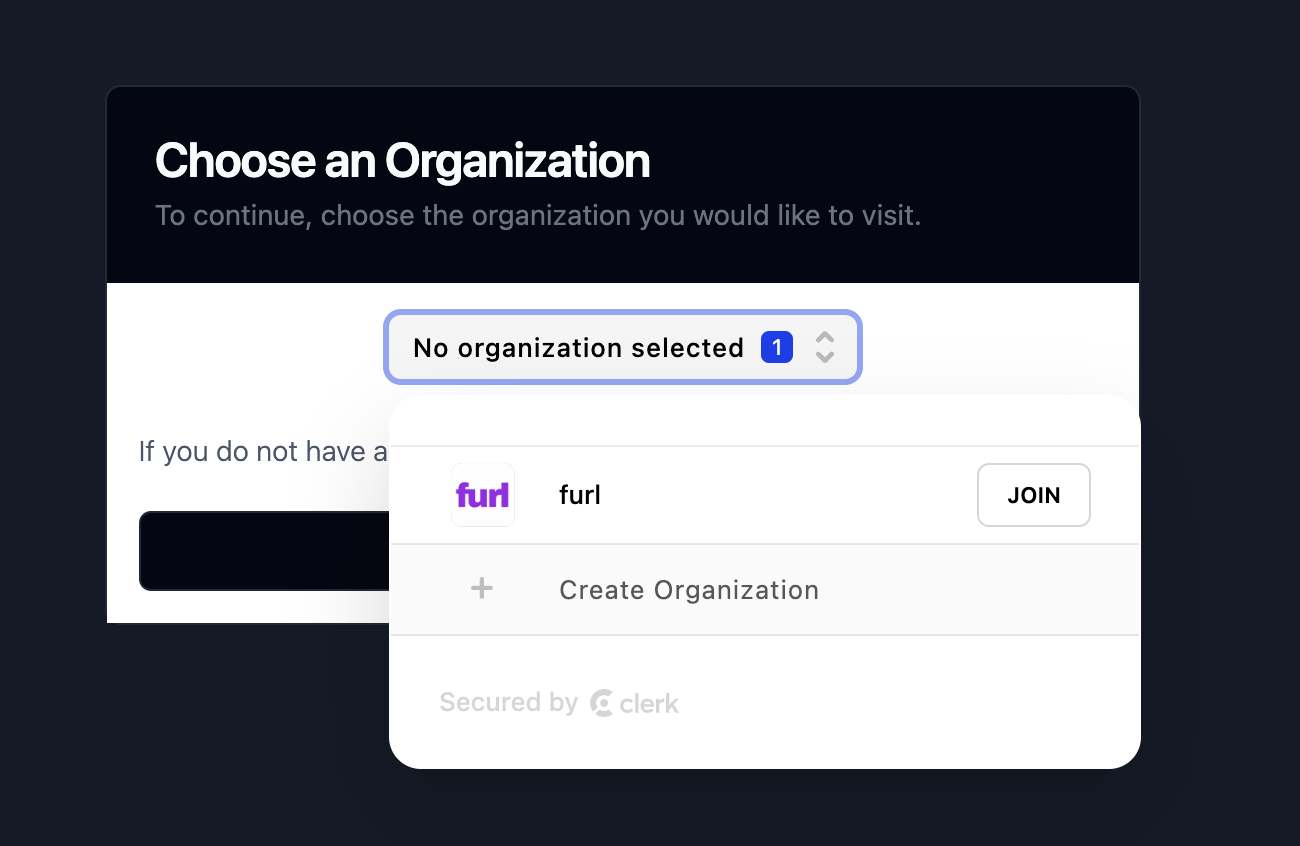
Since users can be members of more than one organization, the first time a user registers they will be prompted to join the organization they were invited to. The first organization they join will now become their default organization the next time they visit furl.
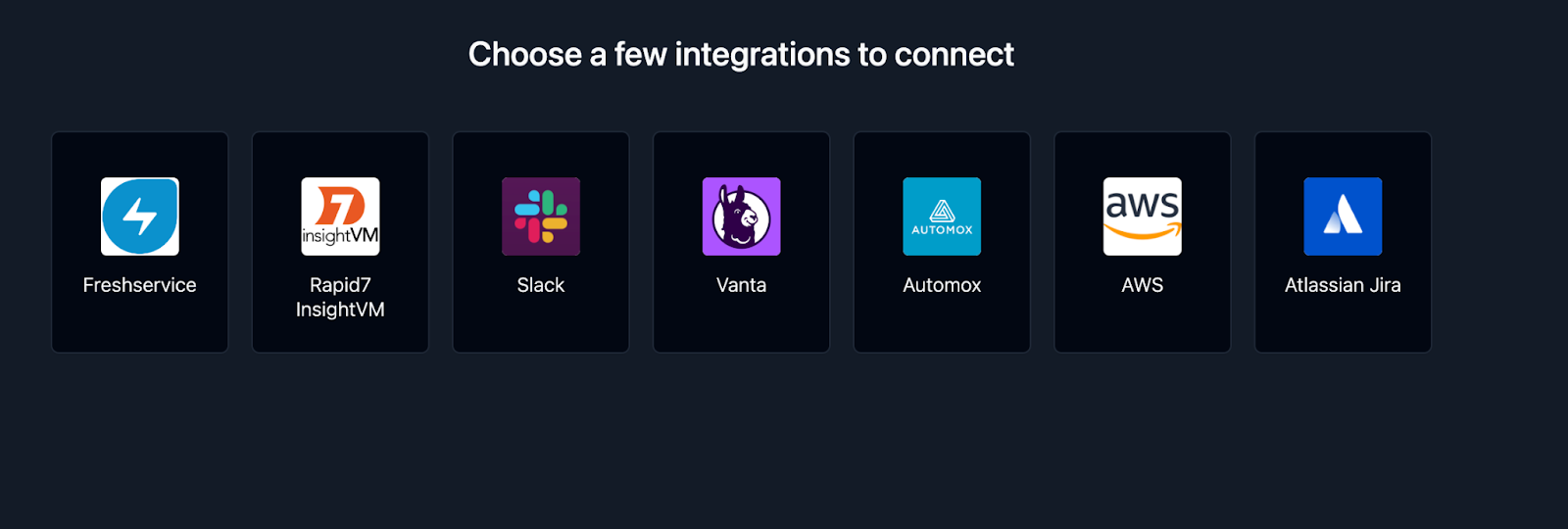
Before exploring furl, it is necessary to perform the initial setup with the third-party tools your organization relies on. Our integrations with vulnerability management tools, asset management tools, ticketing systems, and various others allows us to gain knowledge about your organization in order to begin resolving vulnerabilities and reducing organizational risk.
The first user of an organization must set up at least one integration before continuing. It is highly recommended to begin by setting up the Rapid7 InsightVM integration since vulnerability findings and assets are currently critical for furl resolve vulnerabilities in your environment.
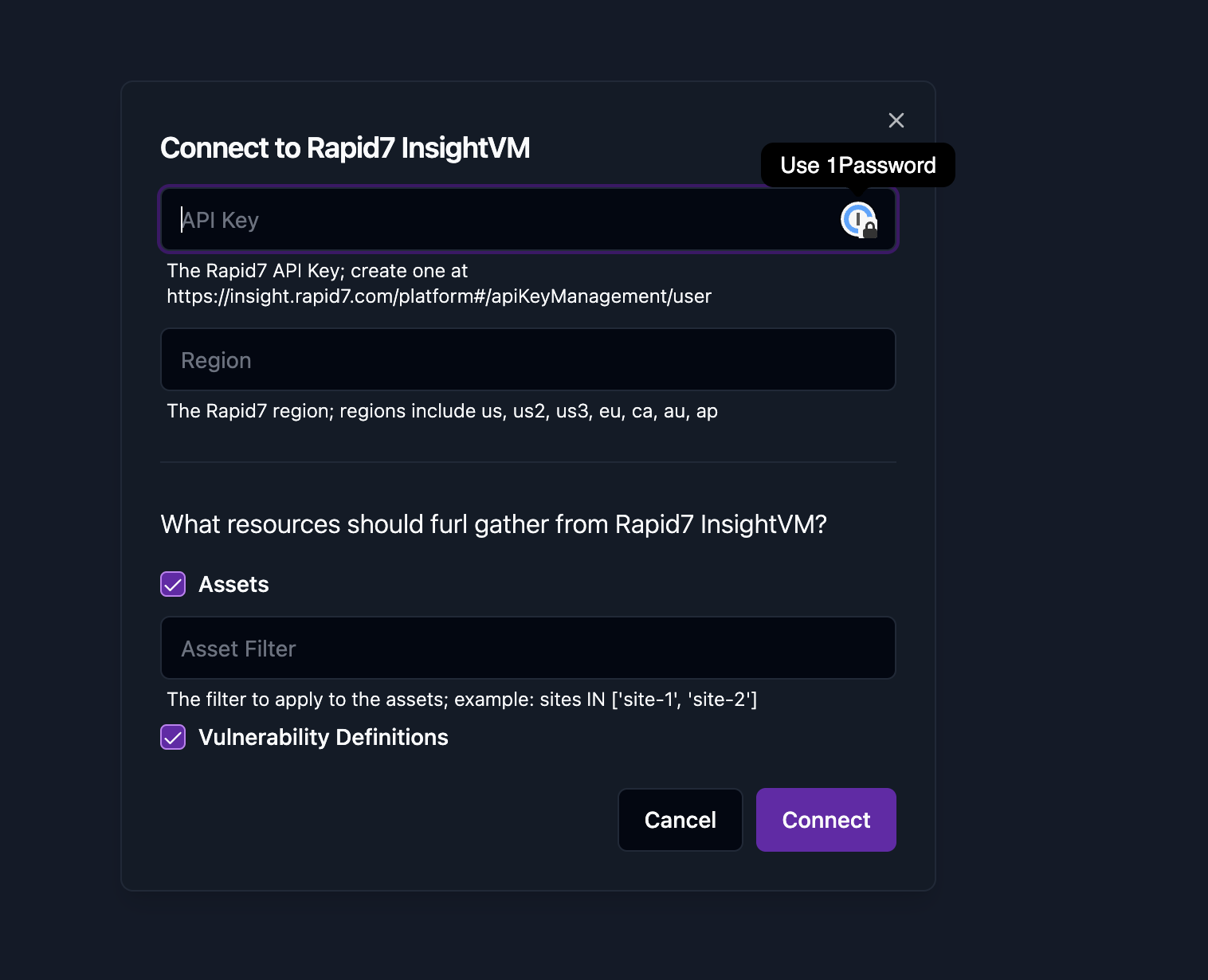
To setup the Rapid7 InsightVM integration, first create a platform API key following the Rapid7 documentation. This API key is used by furl to pull asset and vulnerability findings which are then stored in the furl knowledge graph.
Once the integration setup is complete, it’s time to start prioritizing and reducing your security risk with Furl!
Projects are a way to group, prioritize, and quickly remediate work in furl. They can be used to track and manage the remediation of vulnerabilities, the implementation of new policies, or the resolution of issues.
Once you have connected your organization’s third-party tools, you will be directed to the Projects page where you can create a project by filtering and selecting vulnerable software targets. The project will then be created with the selected targets and furl will determine the best remediation plan to resolve the vulnerabilities. From there you can quickly start the remediation process and track the progress of the project.
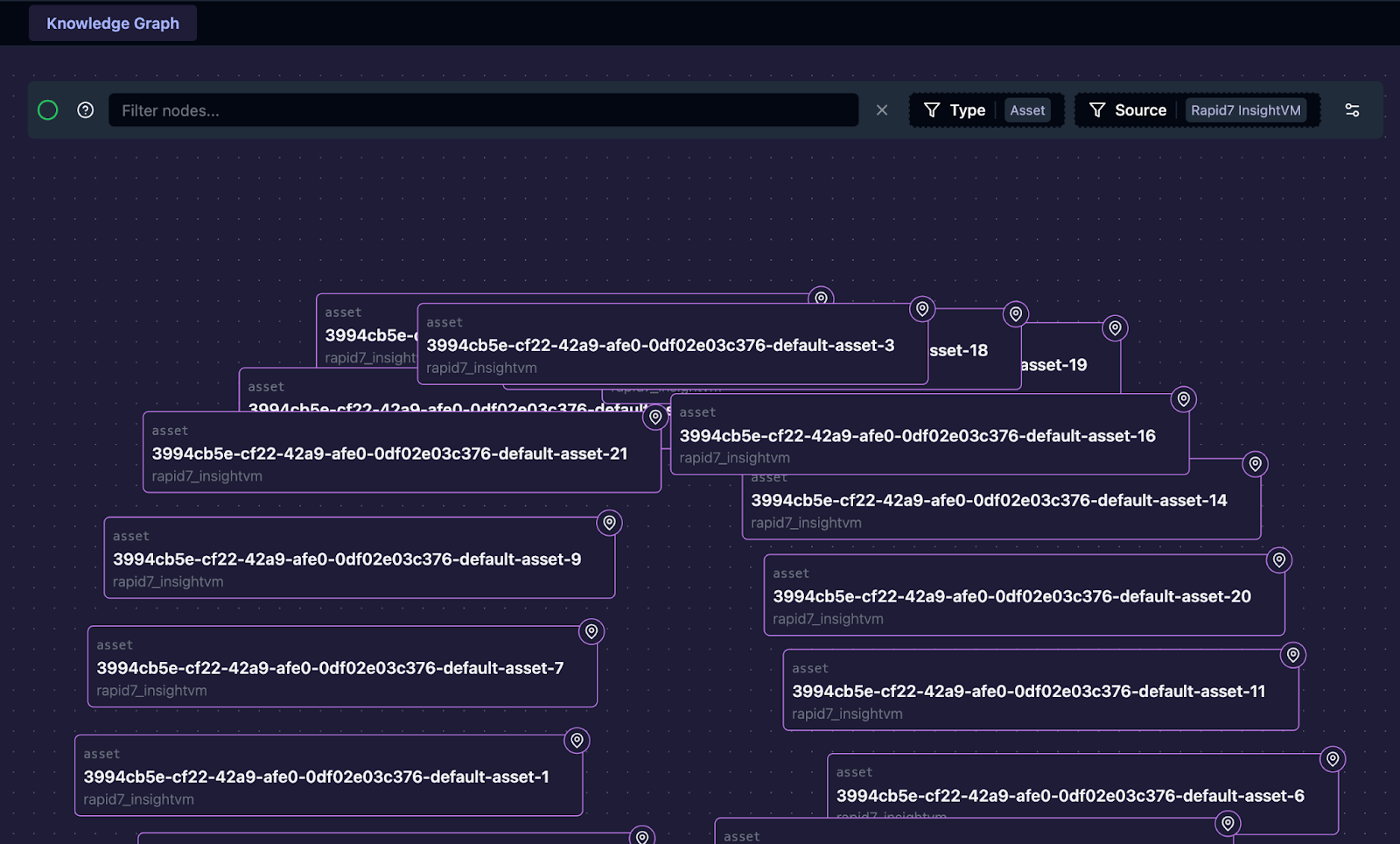
The knowledge graph is a representation of all the data furl has imported aftering connecting to your organization’s third-party tools. It gives a representation of the assets, vulnerabilities, remediation policies, and issues that are all part of a larger picture of what and how issues are remediated for your environment.
From the furl menu, navigate to “Knowledge” which will provide you with a visual graph that can be used to search and visualize data. For example, it’s possible to see only the assets imported from the initially configured Rapid7 InsightVM integration.
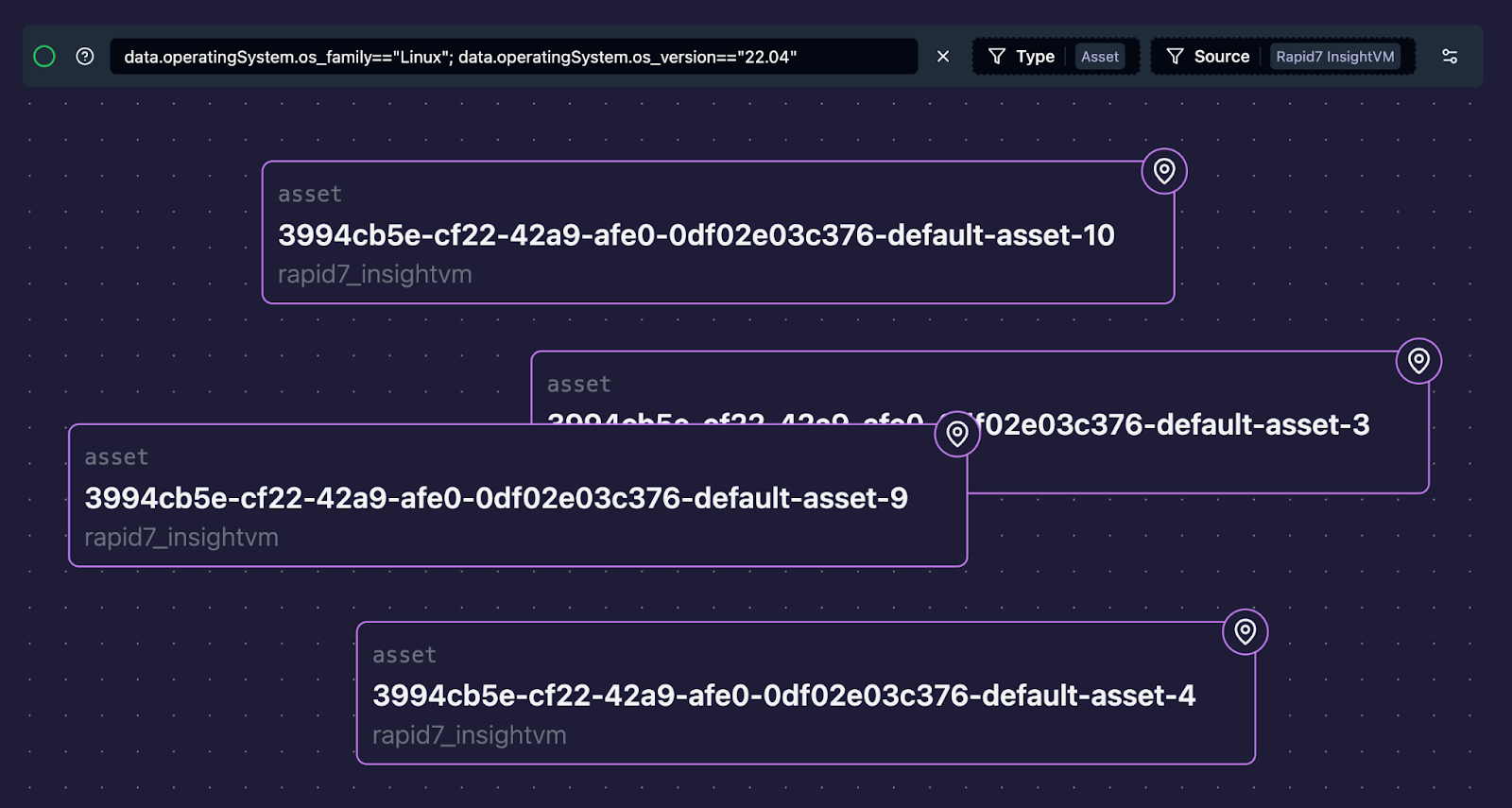
In addition to the type and source filters, its possible to use the filter syntax to be more specific of what should be displayed. It’s possible to return all Linux assets with a version of 22.04 with a filter such as data.operatingSystem.os_family=="Linux"; data.operatingSystem.os_version=="22.04"
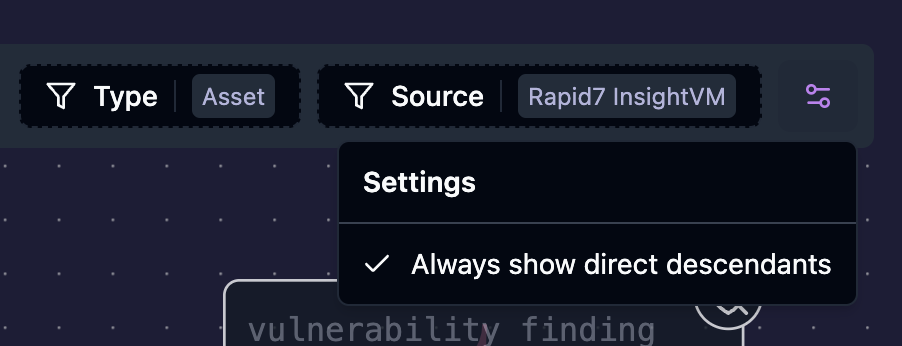
It is also possible to view all vulnerabilities associated with the filtered assets. Enable “Always show direct descendants” in the far right of the filter bar. By viewing the vulnerabilities, it is now possible to see what vulnerabilities are shared between the filtered assets.
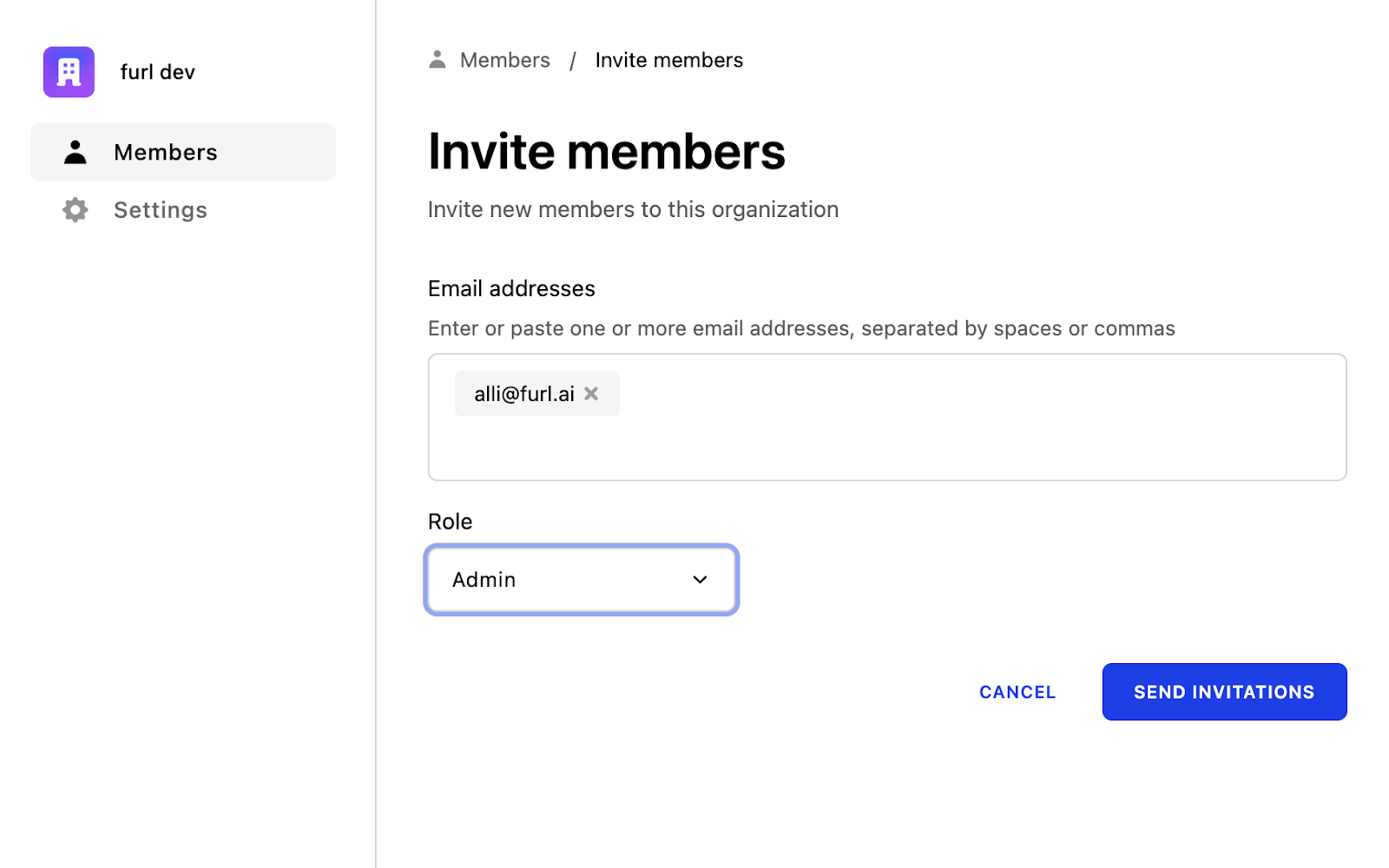
Admins of a furl organization are given the ability to invite additional users to collaborate with. When users are invited to join, they receive the same invitation email and go through the same initial process as the onboarding.
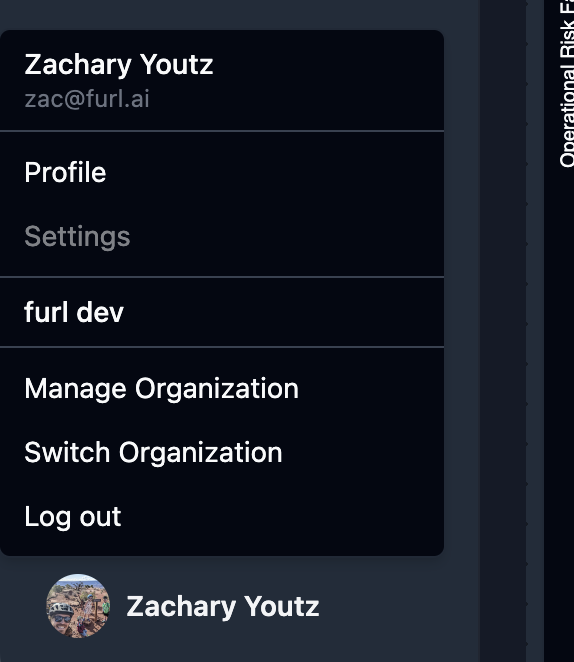
To invite a user to your organization, select “Manage Organization” from your user profile.
From the Invitations tab, invites are able to be sent to new users. It is important to define the correct role for the users when sending invitations. At the moment, the only additional permissions the Admin role is given is the ability to add and remove users to the organization as well as modify the role of other users.